SPriTELab Research Projects
Current Projects

SaTC: Enabling Interdisciplinary Collaboration: Studying Social Engineering Attacks Targeting Vulnerable Refugee Populations
ActiveTwo recent world events, an ongoing pandemic together with continuing regional wars and conflicts, have resulted in a sizable number of refugee population being forcibly displaced and resettled in the United States. Lack of English-language and digital literacy skills have made the refugee community an easy target for new and increased social engineering attacks. This project’s overarching goal is to study how language and linguistic features impact the perception and response of refugees to social engineering attacks. The project’s novelties are a) a language- or linguistic-centric approach for understanding social engineering threats to refugees resulting in development of novel educational materials, open access datasets, and improved cybersecurity policies to counter these threats, and b) tailored digital literacy and educational programs and workshops to raise awareness and mitigate social engineering threats among the refugee population. The project’s broader significance and importance are a) improved protection models and prevention techniques against social engineering attacks, b) informed policies and tools, resulting in better social and economic security, and reduced inequity gap within the vulnerable refugee population, and c) enhanced refugee integration into the U.S. society through increased awareness of cybersecurity threats. The project team systematically study the linguistic cues and triggers associated with social engineering attacks such as phishing and vishing. The deliverables and key contributions of the project include a) preliminary results documenting the impact of linguistic traits of the refugee population on their susceptibility to real-world social engineering attacks, b) open-access datasets of phishing emails, and voice calls, with attributions of interactions to promote further research, c) recommendations to improve cybersecurity policies including vulnerable population, resulting in the creation of new STEM educational material for the refugee population, and d) follow-up educational workshops to debrief, discuss, and disseminate relevant educational material to the target refugee population.

ScooterLab
ActiveScooterLab is a National Science Foundation (NSF) funded community research infrastructure initiative, currently under development at the University of Texas at San Antonio (UTSA). This publicly-available micromobility testbed and crowd-sensing/crowd-sourcing infrastructure will provide researchers access to a community of riders and a fully operational fleet of highly customizable dockless e-scooters. The research team is prototyping infrastructure to be easily retrofitted with state-of-the-art sensors in partnership with collaborators, enableing real-time collection of fine-grained research data from micromobility rides. Website: https://scooterlab.utsa.edu/
A Holistic Context-based Approach for Security and Privacy in the Era of Ubiquitous Sensing and Computing
ActiveThis project plans to uncover new security and privacy risks in modern ubiquitous sensing and computing environments comprising of functionally heterogeneous and isolated sensors and applications and evaluate their feasibility in practical settings. To enable secure and privacy-preserving sensor access by applications, the project will design a novel framework that exposes and harnesses contextual information about users both at the device and network levels for achieving fine-grained and user-approved access control. The first design, called ConWare, will harness the exposed user context at the device level by defining user-approved access bindings between these contexts and the set of allowable sensing actions on that device within those contexts. The second design, called ConWareNet, will harness the exposed user context at the communication network level to regulate applications across an autonomous set of devices using similar user-approved bindings or policies. The project will also address the issue of preventing misuse of the exposed context and will design adaptation mechanisms for these frameworks to self-adjust in a dynamic sensing and actuation environment.
Sub-projects (6)
Background Buster: Peeking through Virtual Backgrounds in Online Video Calls
An Investigative Study on the Privacy Implications of Mobile E-scooter Rental Apps
Acoustics to the Rescue: Physical Key Inference Attack Revisited
Zoom on the Keystrokes: Exploiting Video Calls for Keystroke Inference Attacks
HandwritingAuth: Handwriting-based User Authentication using Wrist-Based Motion Sensors
Light Ears: Information Leakage via Smart Lights
Past Projects
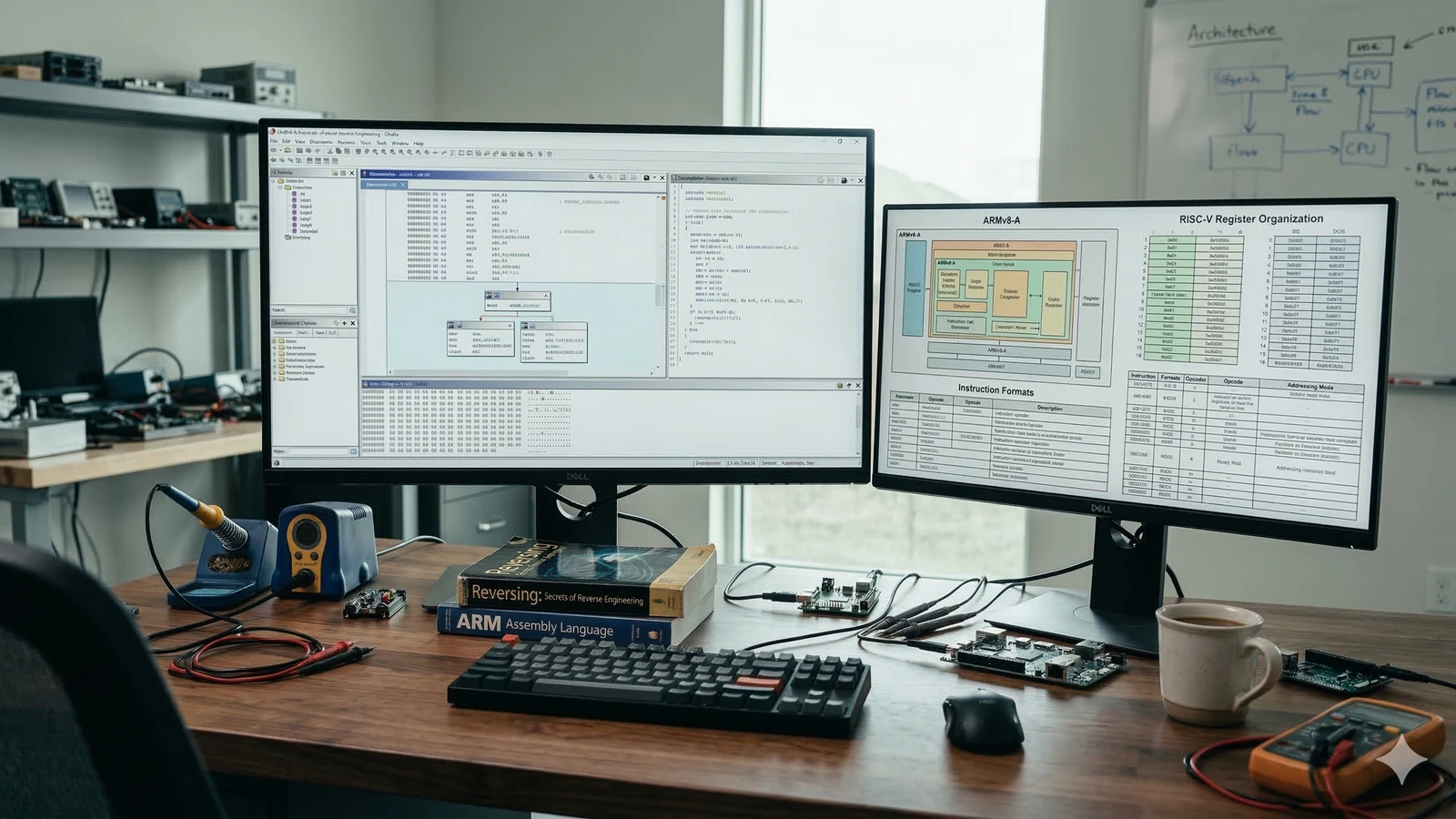
How to Catch a Ditto: Scalable Cross-Architecture Code Comparison on Obfuscated Binaries
CompletedBinary code analysis is the process of analyzing compiled binaries or assembly language code, for example, pre-packaged executable software or firmware, without access to the corresponding source code in order to uncover or match specific functional patterns or signatures. Binary code analysis has various high-impact use cases, such as malware detection, (zero-day) vulnerability discovery, plagiarism detection and runtime crash analysis on the user-end. Prior research efforts that have attempted to address the problem of binary code similarity and containment using either static or dynamic analysis have primarily focused on individual Instruction Set Architectures (ISAs). In other words, these efforts consider or analyze binaries (for similarity and containment) that have been compiled on the same ISA. In this project, we propose Ditto, a new binary code similarity and containment analysis framework that can be universally and efficiently applied to binaries of any ISA, including binaries that may have undergone obfuscation and/or optimization.
Surviving Cybersecurity and Privacy Threats in Wearable Mobile Cyber-Physical Systems
CompletedThe goal of this research project is twofold: first, to demonstrate that wearable devices enable novel side-channel security and privacy threats, and second, to design continuous authentication techniques and adaptive access control mechanisms to survive these threats. Specifically, this research will evaluate private data inference and wearer tracking threats in wearable devices that utilize unprotected sensors as side-channels. This will be accomplished by designing appropriate learning-based classification and prediction mechanisms that can be used by an adversary for inferring sensitive data. On the protection front, this project will develop a multi-sensor activity and identity classification framework. This framework will leverage rich contextual sensor data (e.g., fine-grained movements, application usage and critical body parameters) to enable continuous identification and authentication of legitimate wearers and their activities.
Sub-projects (9)
Analyzing Defense Strategies Against Mobile Information Leakages: A Game-Theoretic Approach
deWristified: Handwriting Inference using Wrist-Based Motion Sensors Revisited
Side-Channel Inference Attacks on Mobile Keypads using Smartwatches
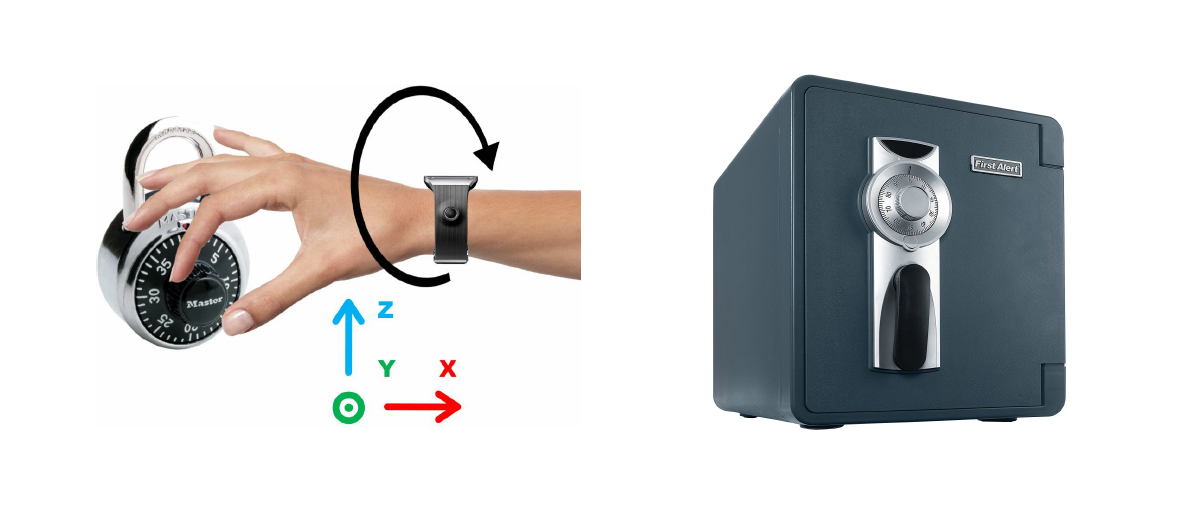
Towards Inferring Mechanical Lock Combinations using Wrist-Wearables as a Side-Channel
Smartwatch-Based Keystroke Inference Attacks and Context-Aware Protection Mechanisms
Keystroke Inference using Ambient Light Sensor on Wrist-Wearables: A Feasibility Study
Information Leakage through Mobile Motion Sensors: User Awareness and Concerns
RandomPad: Usability of Randomized Mobile Keypads for Defeating Inference Attacks
Preventing Shoulder Surfing using Randomized Augmented Reality Keyboards
A Cloud-assisted Framework for Improving Pedestrian Safety in Urban Communities using Crowd-sourced Mobile and Wearable Device Data
CompletedPedestrian distraction continues to be a significant pedestrian safety concern in urban communities. Existing pedestrian safety frameworks and applications are unable to simultaneously detect complex distraction-related activities (often focusing on detecting only specific activities and contexts) and ignore the hazards posed by the distracted pedestrian to fellow pedestrians and drivers. Moreover, a majority of existing complex activity recognition schemes are either computationally impractical for real-time implementation on mainstream mobile and wearable devices, or employ specialized auxiliary hardware, or both. Thus, there is an urgent need for usable and accurate pedestrian safety solutions that can be efficiently implemented (and used) on commercial off-the- shelf (or COTS) mobile and wearable devices. This project proposes a cloud-assisted pedestrian safety framework that detects several commonly observed activities resulting in pedestrian distraction by using multi-modal and multi-source data from users’ mobile and wearable devices, and provides appropriate on-device and community notifications, with the objective of achieving a favorable balance between responsiveness, computational efficiency, detection accuracy and usability.
Sub-projects (2)
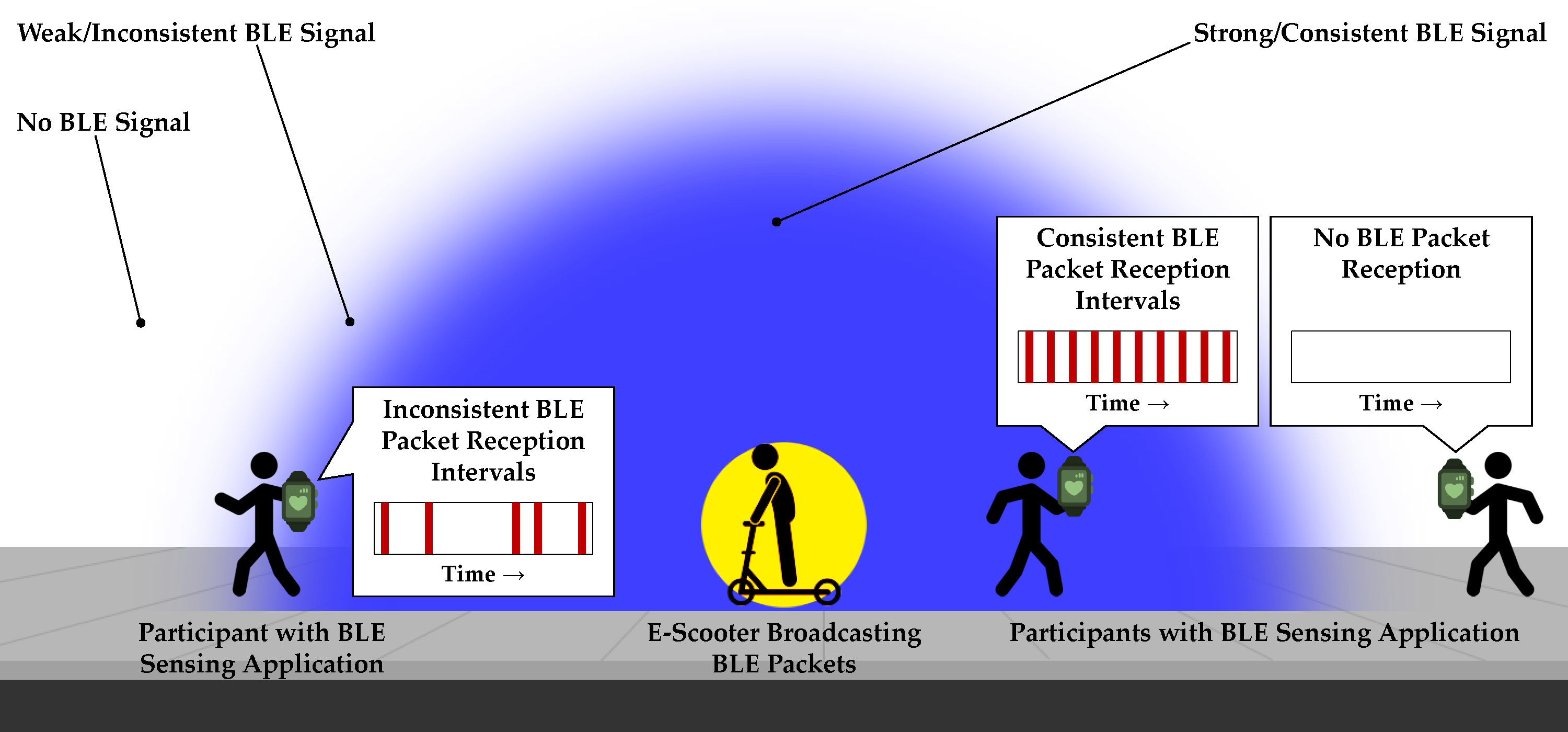
Impact of Urban Micromobility Technology on Pedestrian and Rider Safety: A Field Study using Pedestrian Crowd-Sensing
A Practical Framework for Preventing Distracted Pedestrian-related Incidents using Wrist Wearables
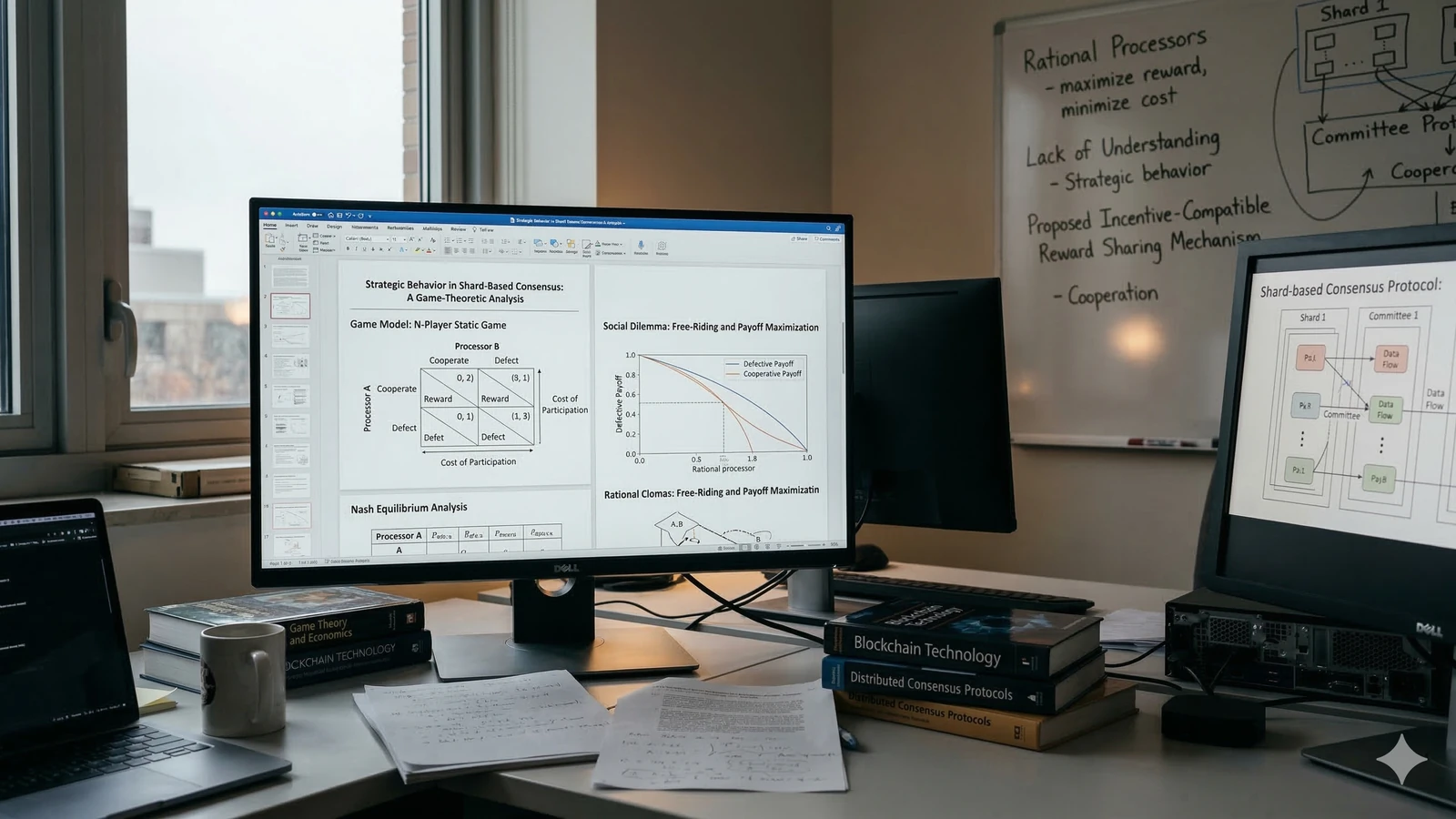
A Game-Theoretic Analysis of Shard-Based Permissionless Blockchains
CompletedOne significant research gap is a lack of understanding of the strategic behavior of rational processors within committees in shard-based consensus protocols. Such an understanding is critical for designing appropriate incentives that will foster cooperation within committees and prevent free-riding. We analyze the behavior of processors using a game-theoretic model, where each processor aims at maximizing its reward at a minimum cost of participating in the protocol. We first analyze the Nash equilibria in an N-player static game model of the sharding protocol. We show that depending on the reward sharing approach employed, processors can potentially increase their payoff by unilaterally behaving in a defective fashion, thus resulting in a social dilemma. In order to overcome this social dilemma, we propose a novel incentive-compatible reward sharing mechanism to promote cooperation among processors.
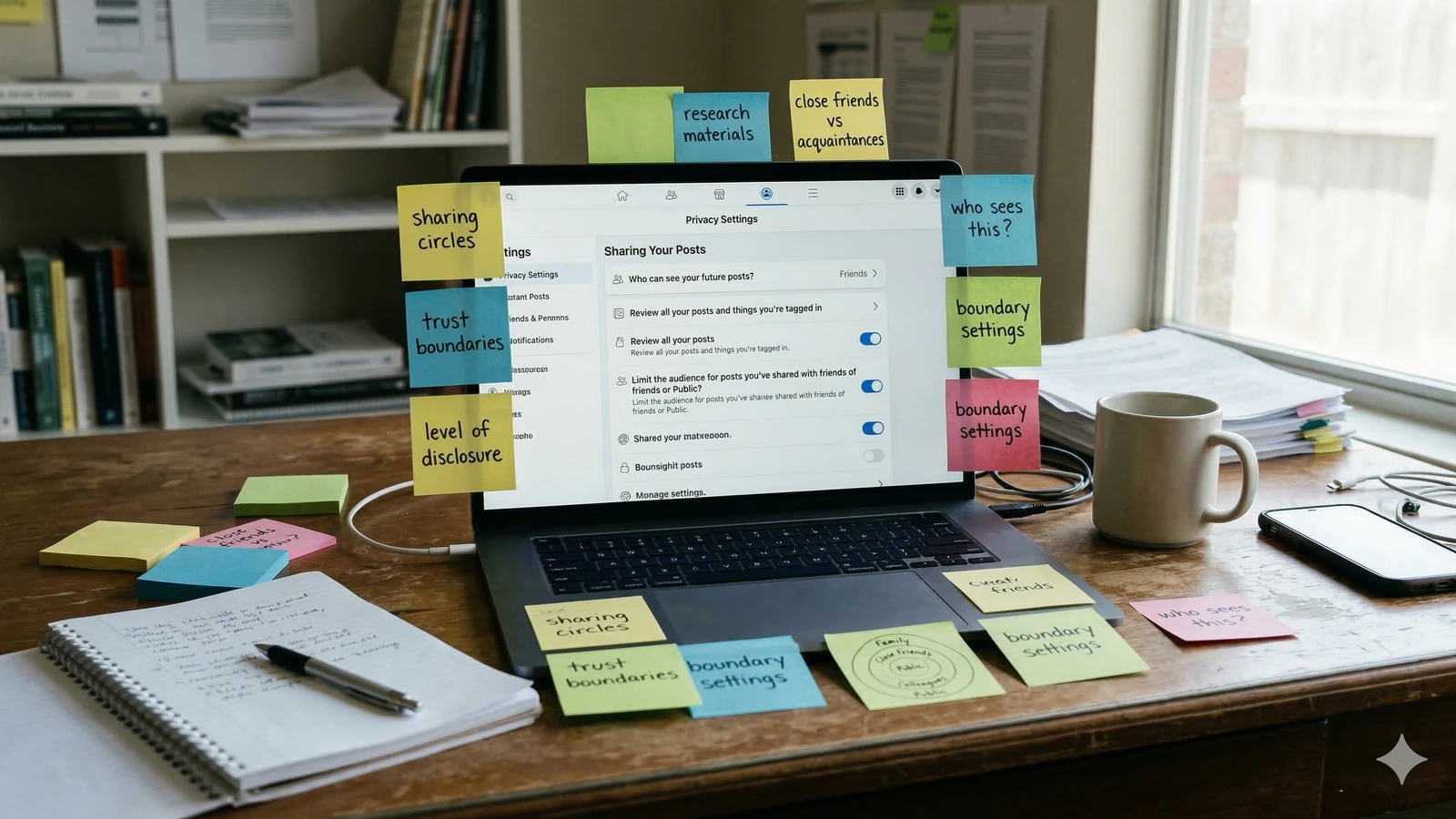
Social Puzzles: Context-Based Access Control in Online Social Networks
CompletedThe increasing popularity of Online Social Networks (OSNs) is spawning new security and privacy concerns. Currently, a majority of OSNs offer very naive access controls that are primarily based on static Access Control Lists (ACL) or policies. But as the number of social connections grow, a static ACL based approach slowly becomes ineffective and unappealing to OSN users. There is an increased need to control access to data based on the associated context, rather than solely on data ownership and social links. Surveillance by the OSN service provider is another critical concern for OSN users, as the service provider may further scrutinize data posted or shared by users for personal gains (e.g., targeted advertisements), for use by corporate partners or to comply with legal orders. In this project, we introduce a novel paradigm of context-based access control in OSNs, where users (in the sharer’s social network) are able to access the shared data only if they have knowledge of the context associated with it.
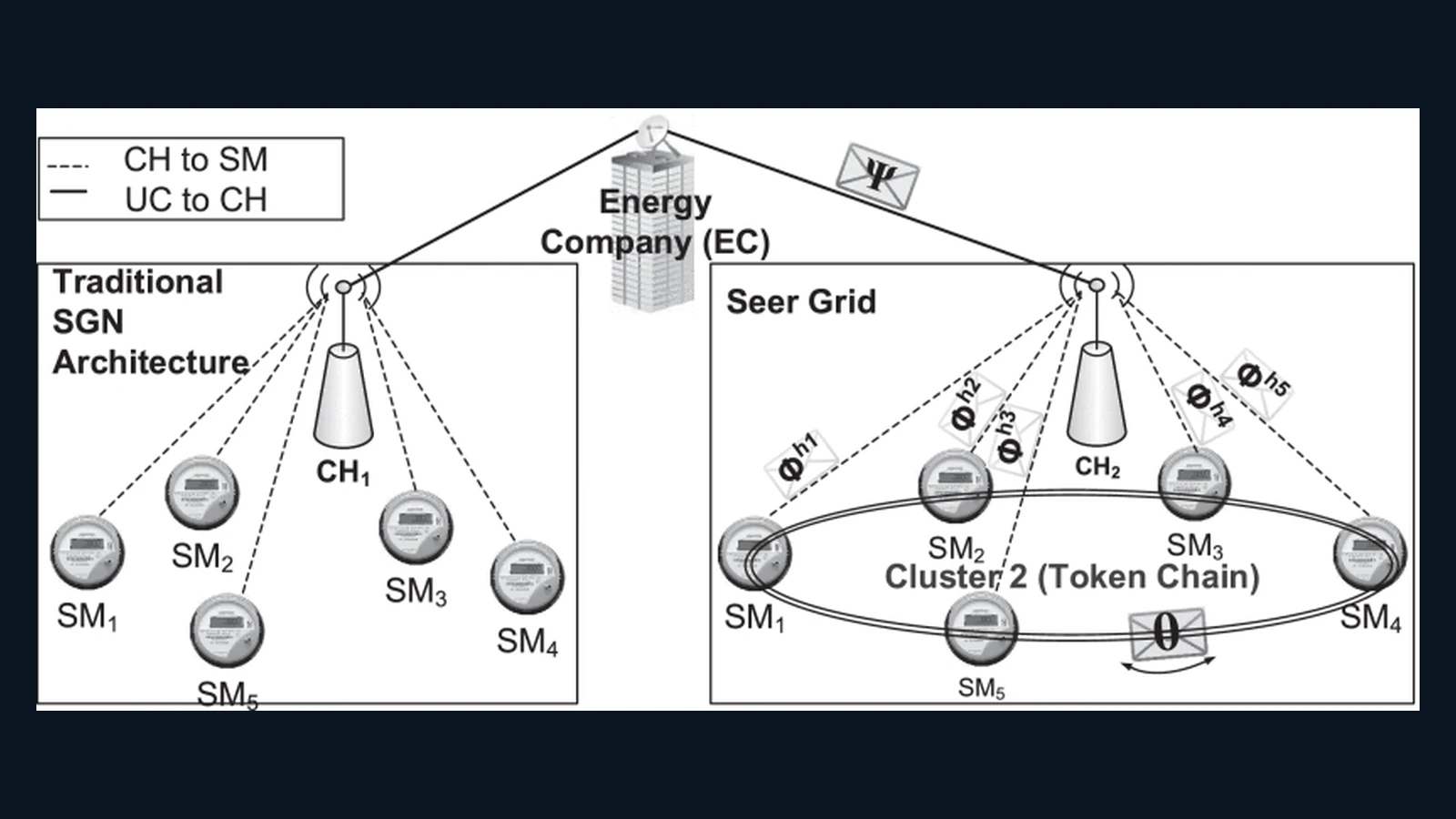
Towards a Privacy-Aware Information-Sharing Framework for Advanced Metering Infrastructures
CompletedSignificant developments in the electric power industry are in the areas of advanced measurements, improved communication infrastructure, renewable energy sources, and electric vehicles. These changes are expected to influence the way energy is provided to and consumed by customers. Advanced Metering Infrastructure (AMI) initiatives are a popular tool to incorporate these changes for modernizing the electricity grid, reduce peak loads, and meet energy-efficiency targets; however, privacy concerns have limited customer acceptance of these initiatives. The research objective of this project is to design appropriate architectures for information collection and dissemination with security and privacy guarantees and to develop state-of-the-art algorithms and protocols for privacy-preserving communication and control that effectively exploit the AMI for improved system operations and active customer participation.
